A few years ago, I had a heartbreaking conversation with a client named Laura. She had spent months designing a unique, sculptural hair claw . To save costs, she split her production. Factory A made the plastic claw body. Factory B made the decorative metal charm. Factory C assembled and packed the final product. Within six weeks of her successful launch, she found her exact design on AliExpress, sold by Factory B. They had simply taken the charm mold they made for her, attached it to a generic claw body, and undercut her price by 60%. By splitting her supply chain, she had inadvertently handed her design blueprint to three different entities, none of whom felt any loyalty to her intellectual property. If you are like Ron, you know that your designs are your brand's most valuable asset. The fear of your unique belt buckle or scarf print appearing on a competitor's website is a constant, nagging anxiety.
Avoiding stolen designs when sourcing from multiple factories requires a strategy of Compartmentalization and Legal Firewalls. You must never provide a single factory with the complete blueprint of your product. Instead, you should separate component manufacturing (molds, stamping, plating) across different, geographically distinct suppliers who are unaware of each other's identities. The final assembly should be handled either by a trusted, vertically integrated partner or by your own internal team. Furthermore, every supplier must sign a robust Mold Ownership Agreement and a Non-Disclosure Agreement (NDA) that is enforceable under Chinese law.
I run AceAccessory in Zhejiang Province. I have seen the dark side of the fragmented supply chain. I have also developed the protocols to protect my clients from it. The temptation to split an order across three factories to save $0.15 per unit is strong. But the cost of that $0.15 savings can be the total loss of your brand's uniqueness. The key is not to avoid specialization. Specialization is good. The key is to control the Information Flow. You must become a master of the "Need to Know" supply chain. Let me walk you through the exact steps to protect your designs when you are forced to work with multiple vendors.
Why Is Splitting Production Across Factories a High Risk for IP Theft?
The moment you share your design file with a factory, you are creating a Digital Asset. In many low-cost manufacturing environments, this asset is viewed as a Commodity to be Monetized, not as sacred client property.
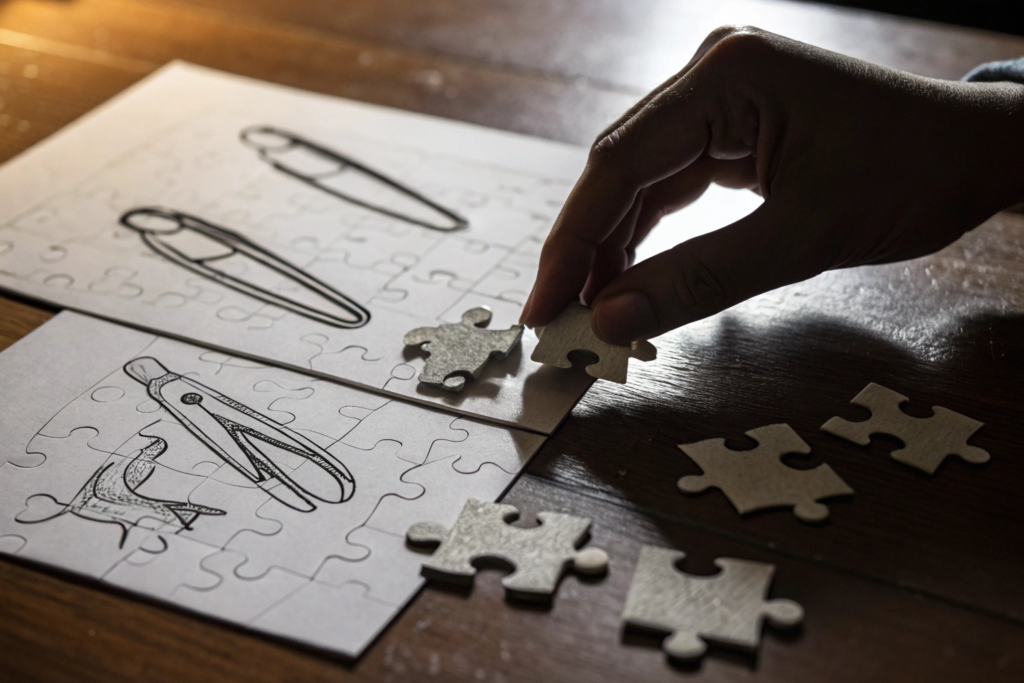
The risk multiplies exponentially when you split production. Here is the core problem: Each factory now has a piece of the puzzle, and they have a financial incentive to complete it.
Let's say you are making a custom belt .
- Factory A (Buckle Maker): They have your CAD file for the unique buckle shape. They know it is a custom item. They know someone paid a mold fee for it. They do not know who the final customer is or what strap it goes on. But they know it's a good design.
- Factory B (Strap Maker): They have your pattern for the leather strap and the stitch design.
- Factory C (Assembly): They see the finished product. They see the packaging.
What often happens is Factory A (the buckle maker) gets a visit from a trading company looking for "new belt designs." Factory A pulls out your buckle sample. The trading company loves it. They ask, "Can you make this with a standard strap?" Factory A says yes. They never mention your name. They just see it as "Another Order."
To prevent this, you must ensure that no single factory possesses the complete, assembled vision of your product. The left hand must not know what the right hand is doing. This is the principle of Supply Chain Compartmentalization. This is how we protect our clients' custom accessories at AceAccessory.
How Does "Design File Creep" Happen in Unsecured Manufacturing Networks?
Design file theft is rarely a dramatic heist. It is usually a slow, careless leak. It happens through "Design File Creep."
- Scenario 1: The WeChat Transfer. A factory salesperson needs to get a quick quote from the plating shop. They export your CAD file to a JPG and send it over WeChat to the plater's personal phone. The plater saves the image. Two weeks later, the plater's cousin, who works for a competitor, sees the cool design on the phone. It gets shared again.
- Scenario 2: The Sample Room Shelf. Factory A finishes your buckle sample. They keep one extra piece on the "Inspiration Shelf" in their showroom. A visiting buyer from a different brand sees it and says, "I want that." The factory owner thinks, "Why not? I already made the mold."
- Scenario 3: The Rogue Employee. A CAD designer leaves Factory A to start their own trading company. They take a hard drive with them. They have every file they ever worked on.
These leaks are nearly impossible to trace back to the source. They happen because the factory lacks Internal IT Security Protocols and Employee IP Training. Most small to medium Chinese factories do not have a dedicated IT security department. Their focus is on production, not cybersecurity.
At AceAccessory, we mitigate this risk through strict internal controls. USB ports are disabled on design computers. Files are shared only via a Secure Cloud Portal with access logging. And our Employee Contracts contain specific, enforceable clauses regarding client IP theft with severe financial penalties. This is the level of security infrastructure required to protect modern designs.
What Is the "One-Stop Shop" Advantage for Design Security?
This is the counter-argument to splitting production. A Vertically Integrated Manufacturer or a Centralized Supply Chain Manager (like AceAccessory) offers a significantly higher level of IP security.
Here is the logic:
- Single Point of Accountability: If your design leaks, you know exactly where it came from. There is no ambiguity. This creates a powerful deterrent. A factory that values its reputation and its long-term relationship with you will not risk leaking your design because the consequences are direct and severe (loss of all future business).
- Controlled Subcontracting: We do use specialized partners for plating or knitting. But we own the relationship. The subcontractor never knows your brand name. They only know AceAccessory's Work Order Number. They sign our NDA. We are the Firewall between you and the component maker.
- Centralized Assembly: The final product comes together under our roof. The component makers never see the finished, branded item. They only see a piece of metal or a piece of fabric.
This model eliminates the "Trading Company Curiosity" risk. A component maker cannot sell a complete design because they have never seen the complete design. This is the most effective, practical IP protection strategy available in the fashion accessories industry. It is one of the primary reasons clients like Ron choose to consolidate their sourcing with us rather than managing a fragmented vendor base.
What Legal Documents Are Enforceable with Chinese Component Makers?
Many Western buyers believe that contracts with Chinese factories are "not worth the paper they are written on." This is a myth. A poorly drafted, English-only contract sent by email is indeed worthless. A Bilingual, Chop-Stamped, Specific Contract is a powerful legal tool in China.
The key is understanding which legal tools work in the Chinese context.
Document 1: The Mold Ownership Agreement (MOA).
This is your most important weapon. It must state, in both English and Chinese:
- Description of Mold: "Steel injection mold for [Product Name], AceAccessory Internal Code #M-2604-01."
- Ownership Clause: "The mold described herein is the sole and exclusive property of [Your Company Name], a company registered in [State, USA]. The Supplier is merely the bailee of the mold for the purpose of fulfilling Purchase Orders."
- Usage Restriction: "The Supplier shall not use, copy, modify, or permit any third party to use the mold for any purpose other than the production of goods for [Your Company Name]."
- Transfer Clause: "Upon written request and settlement of all outstanding invoices, the Supplier shall release the mold to [Your Company Name] or its designated agent within 15 business days."
This document, when stamped with the factory's Official Company Chop (Seal) , is admissible in Chinese court. It establishes a clear property right. It prevents the factory from holding your mold hostage or using it for other clients.
Document 2: The Bilingual Non-Disclosure Agreement (NDA).
This must include specific Liquidated Damages Clause. A vague promise to "not disclose" is hard to enforce. A specific penalty is easier. For example: "In the event of a breach of confidentiality resulting in the public disclosure of the Client's proprietary design, the Supplier agrees to pay liquidated damages of $25,000 USD and refund 100% of the mold fee."
At AceAccessory, we provide these documents proactively. We do not wait for the client to ask. We want the legal clarity. It protects us as well by setting clear boundaries. This is a hallmark of a professional manufacturing partner .

Why Is a "Chinese Chop" More Important Than a Signature?
In Chinese business law, the Company Seal (Chop) carries more legal weight than an individual's signature. The chop is a physical object—a round metal or plastic stamp—that is registered with the government. It represents the legal person of the corporation.
- A Signature: Could be forged. Could be from an employee who was not authorized. Difficult to verify.
- The Official Company Chop: Its use is strictly controlled by the company's legal representative. Its imprint is on file with the Public Security Bureau. A document bearing the company chop is considered a binding act of the company.
Red Flag: If a factory returns a signed agreement with just a squiggle from a salesperson, it is not binding. You must insist on the Official Company Chop. It is typically a round, red stamp with the company's full registered name in Chinese characters around the edge and a star in the center.
At AceAccessory, all legal agreements are executed with our Official Company Chop. We also provide a copy of our Business License which shows the chop registration. This gives our clients confidence that the agreement is enforceable under Chinese law. This is a detail that many buyers overlook, but it is critical for protecting intellectual property .
How Does a "Limited Scope of Work" Clause Prevent Design Reuse?
This is a specific, tactical clause that should be in every Purchase Order and Mold Agreement. It is designed to prevent the factory from making "Slight Modifications" to your design and claiming it is a new design.
A standard NDA might say: "Supplier will not copy Client's design."
A smart factory lawyer will say: "This new design is 15% different. It is not a copy."
To close this loophole, you need a "Derivative Works" or "Limited Scope" clause.
Sample Clause Wording:
"For a period of three (3) years following the date of this Agreement, Supplier agrees not to design, manufacture, or sell any belt buckle or hair accessory that is substantially similar in appearance, configuration, or ornamental features to the Client's Protected Design, regardless of whether such product is created by modifying the Client's mold or by creating a new mold with similar dimensions."
This clause targets the "Clone with a Twist" strategy. It prevents the factory from changing the shape of a flower petal slightly and calling it a new design. It establishes that the Commercial Essence of the design belongs to you.
At AceAccessory, we welcome these clauses. We do not want to make knock-offs of our clients' designs. We want to make your designs, for you. This clarity of purpose is what defines our ethical manufacturing philosophy.
How Can You Compartmentalize Your Supply Chain Effectively?
If you must split production, you must do so Strategically, not Conveniently. The goal is to ensure that no single supplier has enough information to replicate the final, sellable product.
Step 1: Geographic Separation.
Do not use three factories that are all located in the same industrial park. They talk to each other. They share workers. They drink tea together. The "design file creep" is almost guaranteed. Use a buckle maker in Guangdong, a strap maker in Zhejiang, and do the final assembly in-house or at a trusted third location.
Step 2: Identity Masking.
When you (or your agent) deals with Factory A (Buckle Maker), never reveal the name of Factory B (Strap Maker). Do not ask Factory A to ship the buckles directly to Factory B. That gives Factory A the name and address of the entity that is finishing the product. They can then contact Factory B directly to buy the straps and make the full belt.
The Workaround: The Central Consolidation Hub.
You (or your sourcing agent) set up a Neutral Warehouse Address. Factory A ships the buckles to the Hub. Factory B ships the straps to the Hub. A third-party logistics team (or your own staff) receives both, repackages them into a single kit, and sends them to Factory C for assembly. Factory C only receives a pre-packed kit with a work order number. They never see the original packaging from Factory A or B.
This requires more logistics coordination, but it is the only way to maintain information security in a fragmented supply chain. At AceAccessory, we act as this Secure Consolidation Hub for many of our clients. We manage the component sourcing from our trusted network, but we never expose the client's final brand identity or the full product spec to the component makers. This is a core function of our supply chain management service.

Why Should You Never Let Component Makers Ship Directly to Each Other?
This is the single most common, and most costly, mistake in IP protection. It is logistically convenient. It saves one leg of domestic freight. Do not do it.
Let's walk through the exact chain of events that leads to theft when you allow direct shipping:
- You order custom buckles from Guangzhou Hardware Co.
- You order custom leather straps from Dongguan Leather Co.
- To save time, you instruct Guangzhou Hardware to ship the buckles directly to Dongguan Leather so they can be sewn onto the straps.
- The carton arrives at Dongguan Leather. The shipping label says: "From: Guangzhou Hardware Co. To: Dongguan Leather Co. Reference: [Your Brand Name] Belt Project."
- The owner of Dongguan Leather sees this. He now knows exactly who makes the buckles for this attractive new belt design.
- Six months later, Dongguan Leather gets an order for a "similar belt." He calls his contact at Guangzhou Hardware and says, "Send me 500 of those buckles you made for [Your Brand Name]." Guangzhou Hardware, seeing another order, complies.
You have just introduced your suppliers to each other. You have given them the missing pieces of the puzzle. You have paid them to form a partnership that will now compete against you.
The Rule: Always ship components to a Neutral Intermediary. At AceAccessory, our warehouse serves this purpose. We receive the buckles. We receive the straps. We forward the combined kit to assembly. The component makers only see AceAccessory's address. They never learn each other's names. This is Operational Security 101 for fashion accessories .
How Does a Neutral Assembly Partner Protect Your Finished Design?
Even with component compartmentalization, the final Assembly Partner sees the complete, finished product. This is the point of highest vulnerability. You must choose this partner with extreme care.
A Neutral Assembly Partner is a factory whose business model is purely assembly. They do not design. They do not brand. They do not sell. They just put things together. They have no incentive to steal designs because they have no distribution channel to sell them.
Characteristics of a Secure Assembly Partner:
- No Alibaba Storefront: They do not sell finished goods online.
- No "Inspiration Shelf": Their showroom (if they have one) is empty or only shows generic, unbranded capabilities (e.g., "We can sew this stitch type").
- Strict Employee Phone Policy: Workers on the assembly line cannot have personal phones. This prevents photos of the finished product from leaking onto social media.
At AceAccessory, we perform final assembly for many of our clients. Our facility is a Closed-Loop Environment. We do not allow visitors onto the assembly floor when client-specific products are being finished. We take this responsibility seriously because our reputation is built on Trust. This is the final, critical layer in the IP protection framework.
How Do You Use Time-to-Market as a Defense Against Copycats?
The best defense against copycats is not just a legal document. It is Speed. The faster you move from design concept to market saturation, the smaller the window of opportunity for a copycat.
Think about the economics of copying. A factory will only copy a design if they believe there is unmet market demand that they can capture. If you launch your hair claw design in August, and by September you have sold 20,000 units and moved on to the next design, the copycat is left holding a mold for a product that has already peaked. They are late to the party.
This strategy is called "First Mover Advantage on Steroids."
How to Execute a Speed-Based Defense:
- Tight Development Timeline: Compress the sampling and approval phase. Use 3D printing for rapid sign-off. Do not let the project languish in "design limbo."
- Rapid Production Ramp-Up: Work with a factory that can scale quickly. Go from 1,000 units to 10,000 units in a matter of weeks.
- Blitz Distribution: Use air freight for the initial 20% of the order to get it into the hands of influencers and key retail partners immediately. The remaining 80% can come by sea.
- Constant Newness: Have the next design already in the pipeline. By the time the copycat copies Version 1, you are launching Version 2.
At AceAccessory, we are structured for Speed. Our proximity to the Yiwu material market and our in-house mold making capabilities allow us to compress timelines that take other factories weeks. We help our clients execute this Velocity Strategy. We know that a container sitting on the dock is an invitation to a copycat. A product that is already sold out is of no interest to them.

How Does Rapid Reorder Capability Discourage Factory Leakage?
This is a powerful behavioral incentive. If a factory knows that you will reorder this design repeatedly and consistently, they have a strong financial incentive not to leak it.
Why? Because a steady stream of legal purchase orders is predictable income. Selling a few hundred pieces to a shady trading company is a one-time, risky transaction.
If a factory leaks your design to a discounter, two things happen:
- The market price for the item collapses. You, the original brand, can no longer sell it at full margin. You cancel future reorders.
- The factory loses a reliable client. They traded a long-term revenue stream for a short-term, low-margin side hustle.
The Strategy: Structure your orders to demonstrate Long-Term Commitment. Place an initial order for 5,000 pieces. Then, place a follow-up reorder for 3,000 pieces while the first order is still on the water. This signals to the factory owner: "This buyer is serious. This design has legs. I will make more money by keeping this exclusive and fulfilling these reorders than I will by selling a few copies."
At AceAccessory, we value Partnerships over Transactions. We actively look for designs that have reorder potential. We are transparent with our clients: "This color is selling fast. Let's reorder now to secure the production slot." This aligns our financial interest with protecting your design. We make more money when you sell more products .
What Role Does "Constant Newness" Play in Diluting the Value of Old Designs?
This is the strategic layer of IP protection. It is the fashion industry's traditional defense. By the time the copycat has tooled up and produced their knock-off, the Cultural Relevance of the original design has faded.
This is especially effective in fashion accessories where the trend cycle is 6-12 months.
Tactical Application:
- Limited Edition Drops: Market the design as a "Summer Seasonal Exclusive." Create the perception of scarcity.
- Rapid Iteration: Release the same functional item in a new Material or Colorway for the next season. The "Terracotta Sculptural Claw" is replaced by the "Sea Glass Sculptural Claw." The mold is the same, but the market perception is new.
- Discontinue SKUs Publicly: Announce on social media: "Last chance to get the Terracotta Claw!" This clears your inventory and signals to the market that the design is done.
Once a design is publicly "discontinued," its value to a copycat plummets. They are selling a "last season" item. They can only compete on price, and their margins are thin.
At AceAccessory, we support this strategy by offering Low Minimums on New Colors and Flexible Production Scheduling. We enable our clients to maintain a rapid cadence of newness without being burdened by massive inventory of old designs. This agility is the ultimate weapon in the war against copycats.
Conclusion
Protecting your designs when sourcing from multiple factories is a challenge that requires a fundamental shift in mindset. You must move from a mindset of Convenience to a mindset of Security. The logistical shortcuts that save a few dollars in freight are often the very pathways that lead to design theft. By understanding the mechanics of "design file creep" and the incentives of component makers, you can architect a supply chain that minimizes information leakage.
The most effective defenses are a combination of Legal Firewalls and Operational Compartmentalization. A bilingual, chop-stamped Mold Ownership Agreement establishes your legal right. A supply chain structure where component makers never ship to each other, and where a neutral partner handles assembly, prevents the practical ability to copy. And ultimately, a strategy of Speed and Constant Newness renders the stolen design commercially obsolete before the copycat can even get to market.
You do not have to navigate this complex landscape alone. Partnering with a centralized supply chain manager who understands these protocols and acts as a secure firewall can provide the protection of compartmentalization without the administrative headache.
If you are concerned about protecting your next design and want to discuss a secure sourcing strategy, we can share our standard IP protection protocols with you. Contact our Business Director, Elaine. She can provide a copy of our standard Mold Ownership Agreement and explain our internal security measures. Email Elaine at: elaine@fumaoclothing.com










